In ethical hacking and penetration testing, password cracking is crucial in gaining access to a system or a server.
In systems and databases, passwords are rarely saved in plain-text form.
Passwords are always hashed before being stored in the database, and the hash is compared during the verification process.
Depending on the encryption employed, different systems store password hashes in different ways. And if you have hashes, you can easily crack any password.
And in this article, we’ll explore how to crack password hashes using a handy and excellent Hashcat command-line tool.
So let’s get started.
But before that…
What is a Hash function?
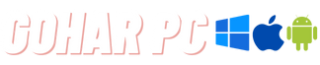
Hashing is the process of converting a normal input text into a fixed-size string of text using some mathematical function which is known as the Hash Function. Any text, regardless of length, can be turned into a random combination of integers and alphabets using an algorithm.
- Input refers to the message that will be hashed.
- The hash function is the encryption algorithm like MD5 and SHA-256 that converts a string into a hash value.
- And finally, the hash value is the result.
What is Hashcat?
Hashcat is the quickest password recovery tool. It was designed to break the high complex passwords in a short amount of time. And this tool is also capable of both wordlist and brute force attacks.
Hashcat has two variants. CPU and GPU (Graphical Processing Unit) based. The GPU-based tool can crack the hashes in less time than the CPU. You can check the GPU driver requirements on their official website.
Features
- Free and open-source
- More than 200 hash type variations can be implemented.
- Supports multi-operating systems like Linux, Windows, and macOS.
- Multi-Platforms like CPU and GPU support are available.
- Multiple hashes can be cracked at the same time.
- Hex-salt and hex-charset files are supported, along with the automatic performance tuning.
- A built-in benchmarking system is available.
- Distributed cracking networks can be supported using overlays.
And you can see other features also from their website.
Installation of Hashcat
First, make sure your Linux system is up to date with the newest programs and tools.
For this, open a terminal and type:
Hashcat is usually pre-installed in Kali Linux. You can find the tool under the password cracking section. But if you need to install it manually in any Linux distribution, type the following command in the terminal.
Tool Usage
To get started with Hashcat, we’ll need some password hashes. If you don’t have a hash to crack, we will create some hashes first.
To create hashes using the command line, just follow the below format.
For example, you can see I turned some words into hashes using the md5 algorithm below.
And the output will be saved in the crackhash.txt file.
Now we will check the hashes which were saved in the given file.
You can see, now we have some hashes to crack. This is the procedure to create a hash by using the algorithm of your choice.
The next step is to kick start a Hashcat tool in your Linux machine. Just use the following command to use Hashcat.
It’ll bring up all of the options you’ll need to know to run the tool. On the terminal, you can find all the attack and hash modes.
The general form of the command is
Here the ‘num’ represents a specific attack and hash mode to use. If you scroll the terminal, you can find the exact numbers for every attack and hash mode, like for md4 – the number is 0, and for sha256 algorithm – the number is 1740.
The wordlist I am going to use is rockyou wordlist. You can easily find that wordlist in the path /usr/share/wordlists.
You can even use the locate command to find that wordlist path.
And finally, to crack the hashes using the wordlist file, use the following command.
After running this command, you may get a runtime error ( Token length exception error ) which can be resolved easily.
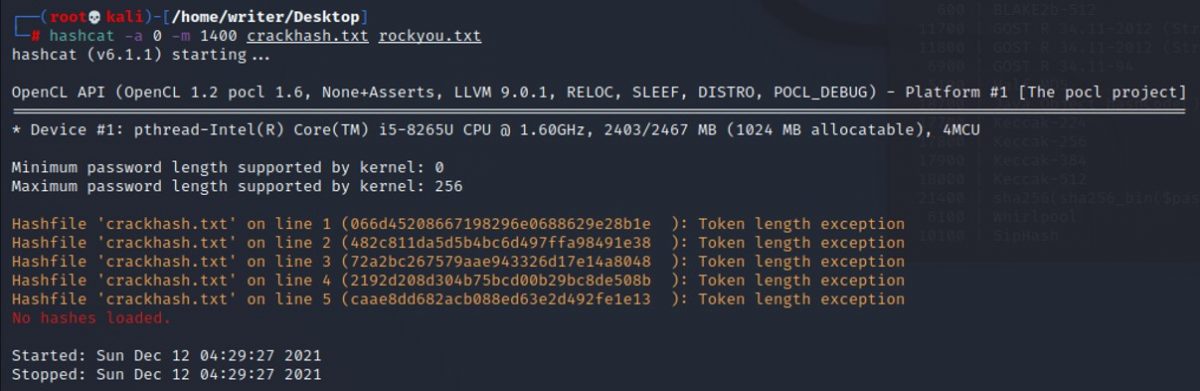
To resolve this, save each hash separately in a different file. This error occurs if you have a low CPU or GPU speed. If your computer has a high-speed processor, you can easily crack all the hashes at the same time as a single file itself.
So after fixing the error and everything, the result will be like this.
In the above result, after the dictionary cache details, you can notice, the hash was cracked, and the password was revealed.
Conclusion
I hope you have gained a better understanding of using Hashcat to crack passwords.